AI in Cybersecurity: Incident Response Automation Opportunities

In today’s digital world, the proliferation of cyberattacks continues to pose complex challenges for businesses. Even the best networks in the world are not immune to cyber incidents. By looking into the first half of 2021 itself, we have witnessed some of the biggest data breaches smashing down the security system of reputed companies in airlines and food & beverages. Such incidents wreak havoc, potentially affecting customers’ data privacy, intellectual properties, company time and resources, and brand value.
According to a report:
- As compared to 2019, in 2021, the total number of malware and ransomware increased by 358% and 435%, respectively.
- Over 100,000 malicious websites and 10,000 malicious files are assessed on a daily basis.
- As of January 2021, over 2 million phishing sites were registered by Google – a 27% increase in 12 months.
(Source: https://www.retarus.com/blog/en/alarming-cybersecurity-statistics-for-2021-and-the-future/)
Taking a proactive approach towards system security management stands as an integral part of threat handling. Knowing how to respond to threat incidents quickly and effectively results in minimizing the breach’s impact.
Incident response plays a critical part in an organization’s security posture by representing the first line of defense in threat handling and developing better risk mitigation approaches for the future. Automating the IR process with artificial intelligence makes it way easier to resolve more incidents at greater speed, less time, and of course, with automation, it’s less effort for the team members.
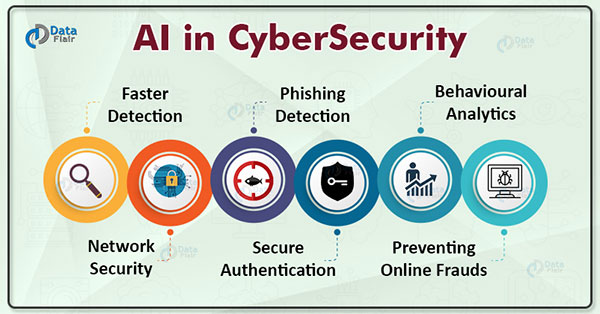
What caused the cybersecurity industry to adapt AI based incident response automation
Remote work system: The geographical distant created due to remote work made it challenging for manual tracking of incidents in IT systems and networks. To overcome such shortcomings and to handle cyber incident response across all regions of operations, cybersecurity experts go for AI automation with intelligent threat detection.
Cost-Effectiveness: Manual threat hunting needs human resources and requires time for analysis. At the same time, AI automation implementation is a one-time cost for the organization while making the incident response easier and quicker.
Reactive nature of cybersecurity: With manual operations, the cybersecurity team could resolve problems only after the cyber incident. Identifying the threat pattern in the system during the dwell time was a major challenge for security experts.
AI in cybersecurity: Incident response
(Source – TechTarget)
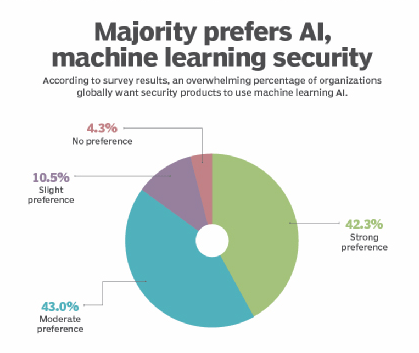
AI technology implementation in cybersecurity is introducing high-security standards and developing better threat prevention and recovery strategies. Some of the key areas where AI implementation has raised the security bars for organizations:
- Threat exposure
- Breach risk prediction
- Data recovery
- End to end system protection
Artificial Intelligence has taken over the cybersecurity space with its quick adaption with the technology platform and 360-degree support for incident detection and handling.
(Source – DataFlair)
Automating Incident response process with AI technology has added enormous value to security operations. With the advanced machine learning feature, AI technology can analyze millions of security events and understand the threat patterns, starting from malware exploiting to risk behavior and phishing attacks to malicious app codes.
With its ability to introduce workflow automation AI has helped the cybersecurity teams to leave out the shortcoming of duplicate security processes followed. Staring from regular security checks to behavior and streaming analytics, active monitoring to intelligent prediction, AI technology has helped overall process completion with 100% efficiency and results.
What are the response automation opportunities available?
- Respond to critical events faster:
Unlike the standard incident response plan, automated IR can monitor millions of security events on a daily basis. With AI automation, Incident handling time is minimized result in timely threat detection and little recovery time. It is considered as one of the primary factors for the effectiveness of incident response automation. - Assigning incident response duties:
Artificial intelligence can automatically make suggestions regarding the allocation of engineers while responding to an incident based on its nature, which is then assessed based on the members’ expertise and availability. - Classify malware and perform risk analysis:
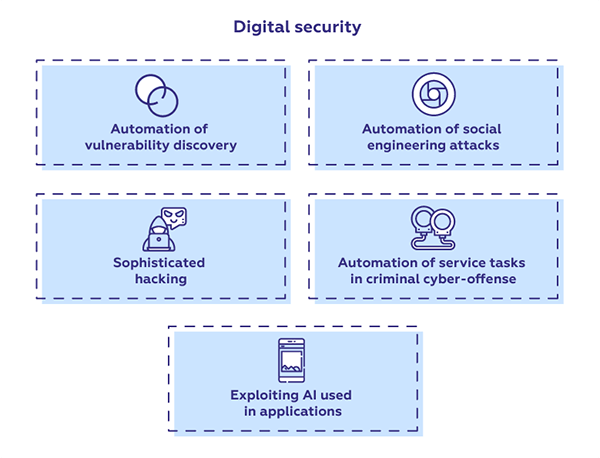
(Source-Sciforce)Artificial intelligence algorithms are developed based on current and past information to identify any anomaly within the regular operations causing unusual events. So that Machine learning can recognize the threat from these patterns and accordingly evaluate and classify malware to perform risk analysis.
- Platform security:
Automated incident response enables a robust platform by seamlessly integrating security protocols into the development process from the initial stages of SDLC. - Better process management:
AI automated incident response process helps you manage security alerts at scale, prioritize all the incident response activities, and ensure that you have the right resources focused on your high-stakes tasks.
While cyber-attacks seem inevitable, with an increase in scale and frequency, the manual nature of today’s incident response methodology slows down the breach detection and necessary response, leaving customers’ data and systems vulnerable to cyber threats. Incident response process automation with AI technology helps businesses fasten up their security investigations and necessary enactments.
SISA’s Incident Response retainership service gives you the freedom to use our expert threat hunting services ranging from Periodic Threat Hunting to First Responder Training, Simulated Attacks, and Forensic Retainership, whenever you need it.
Our forensic team understands an organization’s cyber resilience while handling critical security breaches and conducts 360-degree forensic analysis to perform a necessary containment level against the attack to identify the reason behind the breach and recover the stolen data without any damage.
 USA
USA India
India APAC
APAC Middle East
Middle East Global
Global




 Facebook
Facebook Linkedin
Linkedin  X
X Youtube
Youtube