

The importance of 3D Secure for payments data security
The 3D Secure protocol with enhanced security comes with a host of benefits for merchants, card issuers and customers alike. Besides improving the legitimacy of the firm and strengthening customer loyalty, the biggest benefit of 3D Secure is its ability to decrease fraud while still being simple to use.
As online shopping continues to grow, so does the need for robust payment data security programs. One such measure is 3D Secure (3DS) – a security protocol used for online card transactions to provide an additional layer of authentication. Also known as Payer authentication, 3D Secure verifies the identity of the cardholder by requiring them to enter a password or a one-time code sent via text message or email. This extra step helps prevent unauthorized transactions, reduces the risk of fraud and provides merchants an added peace of mind when conducting online transactions. It is widely used by banks and card issuers to protect their customers’ online transactions. Besides, the implementation of this messaging protocol is governed by regulatory requirements under PCI 3DS Core Security Standard. We often hear about 3DS in the form of “Verified by Visa” or “Mastercard SecureCode.” However different card networks have developed their own 3D Secure transaction products.
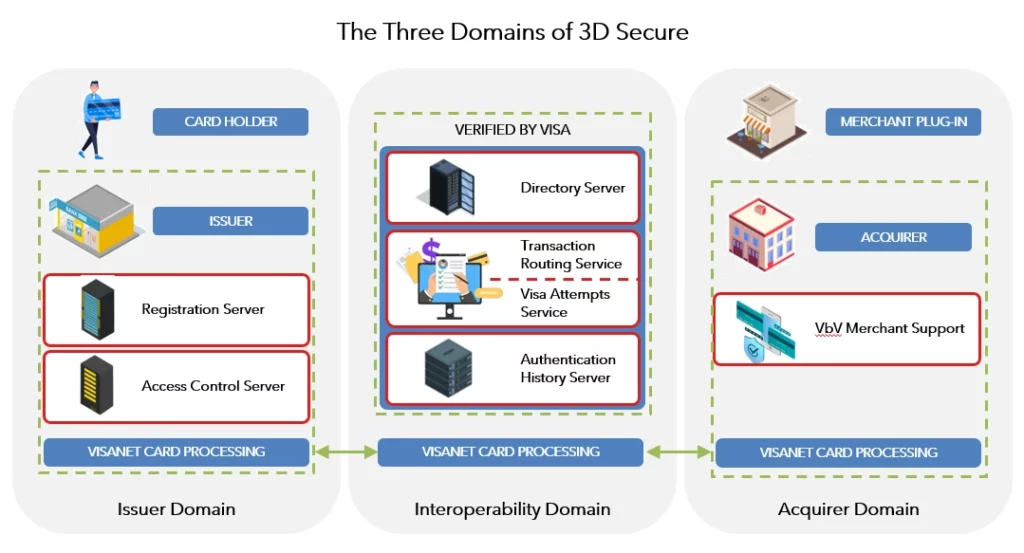
Domains of 3DS
The term 3DS stands for 3 Domain Server because the 3DS transaction involves three parties to act as additional level of payment protection:
The Issuer Domain:
This refers to the organization that issued the card being used in the online transaction. Issuers are responsible for enrolling the card holders in the service through verifying their identity and authenticating cardholders during online purchase.
The Acquirer Domain
This domain pertains to merchant’s banks accepting card payments. Banks must ensure that the merchants operate under a merchant agreement with the acquirer and comply with 3DS requirements. The acquirer domain is also responsible for processing the authenticated transactions
The Interoperability Domain
This domain consists of payment systems that act as connectors between an Acquirer Domain and an Issuer Domains for secure exchange of transactions. This domain decides which network is required for the transaction.
The figure below explains the infrastructure setup in a 3DS enrolment and authentication process.
3D Secure transaction process flow
The 3D Secure authentication uses a combination of XML messages, TLS connections, Digital certificates, and client authentication to confirm the identities of the different domains involved in online transactions.
To understand it better, the 3D Secure process can be broken down into two steps:
1. The Enrolment process
For a customer to perform a 3D Secure transaction, the cardholder must register for the service. The cardholder performs the registration by visiting the issuer enrolment site and enters their unique credit/debit card data. A shared secret is established at this time. The issuer then verifies the cardholder identity and if successful, the shared secret information is stored for later use.
2. 3D Secure Transaction Flow
The second step involves the end-to-end transaction flow, illustrated in the figure below.
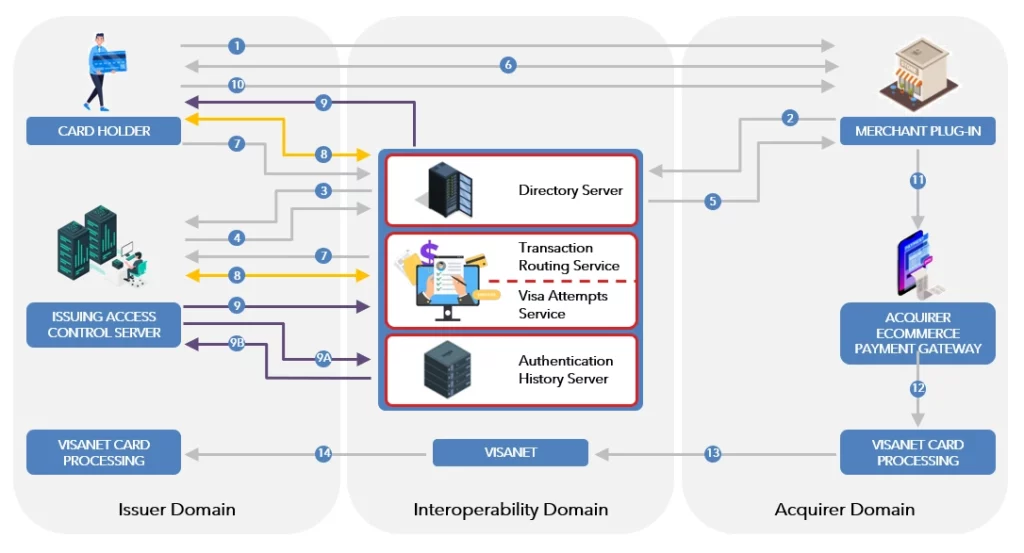
- The cardholder visits a merchant’s website and enters the card information at checkout.
- The merchant’s payment gateway automatically sends transaction details (amount, payment method etc.) and a 3DS 2.0 verification request to the cardholder’s issuing bank.
- The issuer’s Access Control server (ACS) refers to its internal registration records to determine whether the card is registered for 3D Secure services.
- If the card is enrolled in 3D Secure, the issuer initiates the 3DS authentication flow (see below). If the card is not enrolled in 3D Secure, the flow automatically stops, and the user is prompted.
- The issuer determines if the transaction is low-risk and if frictionless authentication is possible, then runs a fraud screening and risk assessment in the background, without input from the consumer. If the issuer determines that a transaction is high-risk, it initiates a challenge authentication flow.
- The cardholder is required to verify their identity using either a one-time authentication code (provided by the issuer) or biometric data. The common identity verification methods include entering a unique password, a security question, fingerprint identification, bank app approval or a URL sent via SMS on the cardholder’s phone. The cardholder receives confirmation of a successful payment on the merchant’s website.
The 3D Secure protocol with enhanced security comes with a host of benefits for merchants, card issuers and customers alike. Besides improving the legitimacy of the firm and strengthening customer loyalty, the biggest benefit of 3D Secure is its ability to decrease fraud while still being simple to use.
Benefits to Merchants and Card Issuers
Liability reorientation
A key benefit that 3D Secure confers on merchants is the Liability Shift rule. If a merchant has enrolled for 3D Secure, and a shopper denies they made or authorized a purchase (lost or stolen card), the liability for the fraudulent chargeback shifts from the merchant to the card issuer. It is noteworthy to mention that the 3D Secure liability shift doesn’t apply to recurring transactions. However, if a merchant does not perform the enablement of 3D Secure, the liability of any fraudulent online transaction is shifted to the merchant.
Lower risk of fraud
With additional layers of security authentication, it’s harder for scammers to commit fraud online. The newer version 3D Secure 2.0 has been vastly improved to provide enhanced fraud prevention features along with better customer experiences compared to its predecessor 3D Secure 1.0. Due to a significant reduction in checkout time and abandonment rates, the major payment brands have shown an agile move toward 3D Secure 2.0 and are almost set to stop support for 3D Secure 1.0. Hence it’s the right time for merchants to move to 3D Secure 2.0.
Improved risk assessment
3D Secure 2.0 lets the merchant send 10 times more data to issuers with each transaction compared to 3D Secure 1.0. Issuers can use this data to make more informed risk assessments of transactions and determine whether the shopper is the legitimate cardholder.
Benefits to Customers
Increased security
3D Secure authorization requires confirmation of identity, code, OTP (one-time-password), etc. from the card issuer. The added layer of security means fraudulent transactions are less likely with 3D Secure, making online payments safer.
Improved experience
3D Secure 2.0 simplifies the payment process. The use of token-based and biometric authentication instead of static password (in 3D Secure 1.0) means less checkout hassle for customers, shorter waiting time, and most importantly, fewer steps when completing the purchase. The frictionless shopping in turn means lower cart abandonment rate resulting in higher trust and satisfaction.
Conclusion
In conclusion, payment data security is critical for any business that accepts online payments and therefore implementing 3D Secure becomes important. Getting started with 3D Secure first requires merchants, acquirers and payment gateways to understand the scope, applicability and technical specifications of the protocol. PCI 3DS training can help payment security professionals develop the skills and knowledge they need to assess and mitigate risks effectively. As a pioneer in payments security and as a leading global Payment Forensic Investigator (PFI), SISA conducts forensic-driven PCI 3DS and PCI DSS Compliance trainings and workshops to educate security professionals and practitioners on every aspect of payment security. The payment data security programs are available in onsite, online, and cohort-based models and can help organizations get started with 3D Secure journey. SISA also provides consulting services around 3D Secure implementation to enable organizations to meet compliance and audits.
To learn more about our training and certification programs, click here.
Latest
Blogs
Whitepapers
Monthly Threat Brief
Customer Success Stories
Recent Blogs

SISA is a Leader in Cybersecurity Solutions for the Digital Payment Industry. As a Global Payment Forensic Investigator of the PCI Security Standards Council, we leverage forensics insights into preventive, detective, and corrective security solutions, protecting 1,000+ organizations across 40+ countries from evolving cyberthreats.
Our suite of solutions from AI-driven compliance, advanced security testing, agentic detection/ response and learner focused-training has been honored with prestigious awards, including from Financial Express, DSCI-NASSCOM and The Economic Times.
With commitment to innovation, and pioneering advancements in Quantum Security, Hardware Security, and Cybersecurity for AI, SISA is shaping the future of cybersecurity through cutting-edge forensics research.
Company
Resources
Quick Links
Copyright © 2026 SISA. All Rights Reserved.
 USA
USA India
India APAC
APAC Middle East
Middle East Global
Global





 Facebook
Facebook Linkedin
Linkedin  X
X Youtube
Youtube







