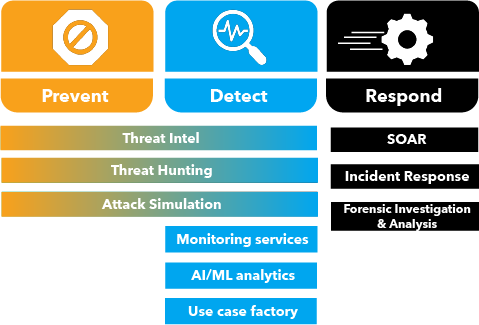
- Whether you are looking for a preventive cyber security solution or a comprehensive, multi-layered defense, SISA ProACT has everything in it to meet your requirement.
- Pay for what you need.
- We understand that each organization’s requirements, devices and volumes are different.
- You can choose between Standard, Advanced and Elite plans to meet your needs and volumes.

 USA
USA India
India APAC
APAC Middle East
Middle East Global
Global





















 Facebook
Facebook Linkedin
Linkedin  X
X Youtube
Youtube








