
Week 5 Threat Advisory on Iran-Israel-US Conflict: Intensifying Cyber Operations and Shift in Identity Weaponization
SISA Sappers Threat Intelligence has been continuously tracking the Iran–Israel–US cyber conflict since its escalation. This advisory is a direct follow-up to our Week 4 Threat Advisory on Iran-Israel-US Conflict: BFSI Cyber Threats Enter Active Phase (25 March 2026) and should be read in conjunction with that advisory.
The US announced a 5-day pause on strikes against Iranian power infrastructure on March 23. A 15-point US peace plan was delivered to Tehran through Pakistan. Tehran publicly denied any negotiations. The war entered its fifth week on Day 28 with ongoing missile exchanges, drone strikes on Gulf infrastructure (Kuwait airport fuel depot struck), and Saudi Arabia continuing to intercept Iranian drones. Iran has not modified its military posture. The cyber campaign will not pause during diplomatic outreach; historical precedent (Operation Ababil, 2012–2013) confirms Iranian cyber operations continue and intensify regardless of back-channel talks.
Five Key Developments
1. Pay2Key hits second US healthcare target – Iran-linked ransomware confirmed
Pay2Key (Iranian government-linked, active since 2020) compromised an administrator account at an unnamed US medical institution in late February, deploying ransomware on March 24. No data exfiltrated, no ransom demanded. Beazley Security and Halcyon confirmed. This is the second confirmed Iran-linked attack on a US healthcare organisation since the conflict began.
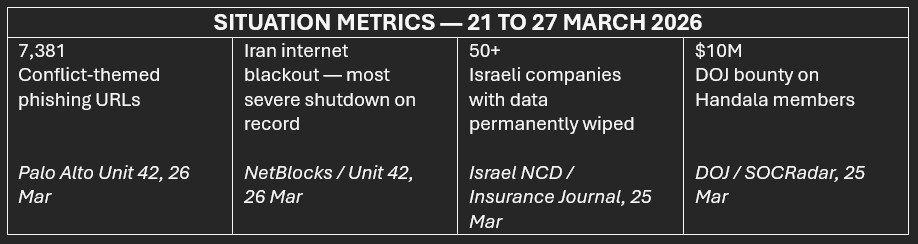
2. DoJ places $10M bounty on Handala members; Handala retaliates with $50M counter-bounty
The US Department of Justice formally announced a $10M reward for information on Handala members, escalating the legal/law enforcement dimension established by the March 20 domain seizure. Handala responded on Telegram with a $50M offer for anyone who ‘eliminates’ Trump and Netanyahu — framed as direct retaliation, raising physical security concerns for named individuals.
3. US State Department launches Bureau of Emerging Threats
Formally stood up March 23 (Congressional notification March 21), the new bureau consolidates five divisions: Cybersecurity, Critical Infrastructure Security, Disruptive Technology, Space Security, and Threat Assessment. The first meeting was held with French Ambassador for Digital Affairs on March 24. The launch signals a structural, long-term US government cyber posture shift, not a temporary conflict response.
4. Handala publishes Israeli Power Grid Schematics and Mossad Targeting Intelligence
On March 25, Handala published nine detailed schematic maps of Israeli power plants and electrical grid layouts. The same day, the group released 14GB of alleged documents on former Mossad head Tamir Pardo (‘From Hunter to Hunted’ post). No breach claimed on the grid — pure ISR targeting intelligence distribution, which demonstrates systematic preattack groundwork against critical infrastructure.
5. Unit 42 confirms Iran’s tactical shift to identity weaponization, bypassing traditional EDR
Palo Alto Networks Unit 42 published updated technical analysis (March 23–26) confirming Void Manticore (Handala) has shifted from compiled wiper binaries to native Microsoft administrative tool abuse. The analysis reveals, 7,381 conflict-themed phishing URLs have been identified across 1,881 unique hostnames. UAE/Emirates-branded financial fraud domains targeting BFSI sector have been confirmed, which indicates traditional endpoint detection tools are insufficient against this vector.
Iran’s Identity Weaponization Shift: Impact Analysis
The Unit 42 confirmation that Void Manticore (Handala) has shifted from compiled wiper malware to native administrative tool abuse is the most strategically significant technical development of Week 4. It fundamentally changes the detection surface BFSI organisations must defend against and invalidates assumptions built into most existing IR runbooks. This has five broad implications.
- EDR is insufficient for this attack class: Attackers using legitimate Intune and Entra ID admin tools generate no malware execution alerts. Conventional endpoint detection will not catch the initial wipe command. Behaviourbased identity monitoring is now mandatory, not optional.
- Admin credential = wiper deployment: A single compromised Global Admin or Intune Administrator credential can wipe every enrolled device globally. The Stryker incident (200,000+ devices) is the proof of concept. The blast radius from one credential is organisation-wide.
- Phishing is the primary initial access vector: 7,381 conflict-themed phishing URLs confirms credential harvesting is running at scale. The shift to identity weaponization makes harvested admin credentials enormously more valuable to attackers than in prior campaigns.
- UAE financial sector is a confirmed active target: Emirates-branded fraud domains and Saudi credential phishing confirm Gulf-based BFSI organisations are within the active campaign scope, not theoretical targets.
- The attack class will proliferate: Once Handala’s Intune abuse technique was publicly confirmed, it entered the broader hacktivist coalition’s toolkit. Other Electronic Operations Room members will adopt the same vector against targets the Stryker attack demonstrated are vulnerable.
Threat Outlook
As the conflict enters its fifth week, the threat landscape is shifting from signals to execution. A temporary pause in kinetic strikes is not de-escalation but a likely pivot toward cyber as a primary lever of pressure. At the same time, observed activity is moving beyond reconnaissance into early-stage destructive operations, consistent with known Iranian campaign playbooks. The following outlook outlines the key inflection points shaping this next phase of the conflict, and what they signal for imminent cyber risk.
Diplomatic Signal: Pause ≠ Ceasefire
Trump’s 5-day pause on strikes against Iranian power infrastructure (announced March 23) and the US-authored 15-point peace plan delivered via Pakistan represent the first meaningful diplomatic overture of the conflict. Tehran has publicly denied the existence of negotiations. However, the mere existence of a peace framework shifts the strategic calculus: if kinetic operations pause, cyber operations will intensify as Iran’s primary remaining instrument of leverage. Historical precedent is unambiguous — Iranian APT groups (APT33, APT34, MuddyWater) were most active during prior diplomatic negotiations, using cyber operations to maintain pressure without triggering kinetic retaliation thresholds. BFSI organisations should treat the current diplomatic window as a period of elevated, not reduced, cyber risk.
The Execution Phase Is Beginning
Akamai’s Week 3 data showed the majority of activity as reconnaissance and credential harvesting. Week 4 shows the transition: confirmed wiper attacks on two US healthcare organisations, Israeli power grid schematic publication, and identity weaponization delivery. The pattern is consistent with Iranian cyber campaign doctrine observed in Operation Ababil (2012–2013) and the SHAMOON campaigns (2012, 2016, 2018): extended reconnaissance followed by concentrated destructive operations. Organisations that have observed elevated scanning, unusual login attempts, or phishing campaigns in the past 21 days are now in the window for destructive followon action. Treat the current period as immediate pre-attack, not preparation phase.
APT Recovery Approaching Critical Threshold
Iran’s internet blackout enters Day 27 at below 1% connectivity — the most severe sustained national shutdown on record, per NetBlocks. State-sponsored APT groups (MuddyWater, APT34, APT33, APT35) remain operationally suppressed within Iran. However, three factors are changing this calculus: (1) pre-positioned access established before the blackout (MuddyWater on US bank, confirmed Symantec/Carbon Black) is now actionable without connectivity restoration; (2) the 15-point peace plan, if accepted, will accelerate Iranian connectivity restoration as a condition of negotiations; (3) satellite connectivity via Starlink — confirmed for Handala since January 2026 — is available to MOIS cells, not just hacktivist proxies. APT capability recovery is not contingent on domestic ISP restoration. It is contingent on MOIS operational decisions.
The Proxy Coalition Is Self-Sustaining
The CSIS assessment published March 25 documents what SISA has assessed since Week 1: the Electronic Operations Room has created a proxy coalition that operates autonomously from Iranian command-and-control. Cyber Fattah’s pre-operational announcement this week (‘collecting specific resources’ before ‘all types of attacks’) signals an independent operational tempo that does not require MOIS authorisation. The DOJ’s $10M bounty on Handala members, while a significant legal escalation, will not reduce the coalition’s operational capacity — it will accelerate the transfer of capability to proxies outside US legal reach, operating from jurisdictions where DOJ warrants are unenforceable. BFSI organisations should plan for a sustained campaign measured in months, not weeks, and should not assume a ceasefire will reduce the hacktivist coalition’s activity to pre-conflict levels.
Revised Defensive Priorities – Week 5 Additions
This section of the advisory outlines new actions only. Actions 1–7 actions from prior advisories remain valid.
1. Audit Intune and Entra ID privileged accounts — identity weaponization is now the confirmed primary attack class.
Unit 42 confirmed that Void Manticore achieved the Stryker wipe via a single compromised Global Admin credential used to issue remote-wipe commands through Intune. Audit: (1) list all Global Admin and Intune Administrator role holders; (2) confirm each account has FIDO2 or certificate-based phishing-resistant MFA; (3) remove all users not requiring Global Admin; (4) enable Privileged Identity Management (PIM) just-in-time access for Intune Administrator roles; (5) review Conditional Access policies for breakglass accounts. An attacker with one compromised admin credential can wipe your entire enrolled device fleet in minutes.
2. Implement Intune device wipe monitoring and require human approval for bulk wipe commands.
The Stryker attack used Intune’s legitimate wipe functionality as a weapon. Microsoft Intune does not natively alert on bulk wipe events in real time. Configure: (1) alert on any
Intune wipe command affecting 5+ devices within 60 minutes; (2) require MFA step-up authentication before any device retirement or wipe command; (3) configure audit log export to SIEM for all Intune administrative actions; (4) test these alerts — many organisations discover monitoring gaps only during the incident. Validate your SIEM has Intune audit log coverage before you need it.
3. Deploy brand monitoring for Emirates, Dubai, and GCC financial institution impersonation domains.
Unit 42 identified active UAE/Emirates-branded fraud domains targeting BFSI customers: asset management sites, banking portals, and cryptocurrency investment scams. These are customer-facing attacks, not internal ones. Deploy: (1) automated monitoring for new domain registrations containing your institution’s name or variants; (2) alert on registrations using your SWIFT BIC, UAE Central Bank licence number, or common brand abbreviations; (3) set up Certificate Transparency log monitoring for SSL certificates issued to lookalike domains; (4) brief customer service teams on the impersonation campaign and update fraud communications.
4. Expand executive and physical security assessment to include Handala’s personal targeting profile.
Handala’s publications this week — the Tamir Pardo 14GB doxx and the $50M counterbounty on named political figures — confirm the group is conducting systematic personal targeting operations. The DOJ bounty announcement increases the likelihood of retaliatory personal targeting of US law enforcement officials and executives at firms that have cooperated with FBI/DOJ investigations. Review: (1) which of your senior executives have been named in public DOJ, FBI, or CISA filings; (2) which executives’ personal details are discoverable through open-source intelligence; (3) update home address and physical security protocols for CISO, CEO, and GC.
5. Review power grid and physical infrastructure continuity plans for Israeli, GCC, and European data centres.
Handala’s publication of Israeli power plant schematics signals preparation for critical infrastructure attacks. BFSI organisations with Israel-based data centres, co-location facilities, or trading infrastructure should assess: (1) power redundancy for primary data centre locations; (2) failover activation time if primary facility loses power; (3) treasury and trading desk continuity from non-Israel locations; (4) generator fuel reserves and maintenance schedules. Update these plans — do not assume physical infrastructure disruption belongs only to kinetic operations.
6. Track Stryker 15-day restoration timeline as the benchmark for your own wiper IR planning.
Stryker entered Day 15 of partial (not full) restoration on March 25. This is the first public, large-scale dataset on recovery time from an identity-weaponization wiper attack on enterprise infrastructure (200,000+ devices, 79 countries). Use it: (1) if your organisation has comparable Intune enrolment and Azure AD dependency, assume a minimum 15-day partial restoration; (2) test whether your backup infrastructure can support that timeline; (3) confirm your cyber insurance policy covers 15+ days of partial operational disruption; (4) brief your Board with a concrete recovery time estimate, not a theoretical range.
7. Add the DOJ Handala bounty confirmation to your OFAC compliance training and IR runbook.
The formal DOJ designation of Handala as MOIS — now in public court documents and backed by a $10M reward programme — means that any BFSI employee involved in incident response who engages with a Handala demand must immediately recognise this as an OFAC SDN interaction. Update: (1) IR runbook with explicit Handala = MOIS = SDN designation; (2) SOC playbook with escalation trigger if Handala attribution is suspected; (3) ensure legal counsel’s OFAC screening checklist includes Handala, Sicarii, and associated aliases; (4) brief your Board that victim organisations carry sanctions liability regardless of the nature of any payment.
Sources & References
- Palo Alto Networks Unit 42 — March 2026 Iran Escalation Threat Brief (updated March 26, 2026)
- Unit 42 — Technical analysis of Void Manticore identity weaponization and Intune abuse vector (March 23–26)
- Halcyon — Pay2Key ransomware analysis and malware samples (March 24)
- Beazley Security — Pay2Key incident response report (March 24)
- SOCRadar — Iran–Israel Cyber Conflict Dashboard (March 25 update — Handala Pardo doxx, power grid schematics, counter-bounty)
- US State Department — Bureau of Emerging Threats formal launch announcement (March 23)
- CSIS Strategic Technologies Program — ‘How Will Cyber Warfare Shape the US–Israel Conflict with Iran?’ (March 25, 2026)
- Bloomberg (15-point US–Iran peace plan via Pakistan, March 25)
- Times of Israel (Iranian missile targets Israeli power plant, March 25
 USA
USA India
India APAC
APAC Middle East
Middle East Global
Global

 Facebook
Facebook Linkedin
Linkedin  X
X Youtube
Youtube








