
Week 4 Threat Advisory on Iran-Israel-US Conflict: BFSI Cyber Threats Enter Active Phase
SISA Sappers Threat Intelligence has been continuously tracking the Iran–Israel–US cyber conflict since its escalation. This advisory is a direct follow-up to our Week 3 assessment — Iran–Israel–US Escalation: Week 3 Assessment (18 March 2026) and should be read in conjunction with that advisory.
In the week since that publication, the threat environment for BFSI organisations has not merely continued — it has escalated across five distinct dimensions. What was assessed as high probability in Week 3 is now confirmed and declared. These are not incremental updates — they represent threshold events that demand immediate re-evaluation of your organisation’s defensive posture, regardless of geography or perceived exposure.
What Has Changed: Five Critical Events Elevating Cyber Risk for BFSI
1. DOJ/FBI seizes Handala’s 4 primary domains on March 20— first major US counter-cyber action of the conflict.
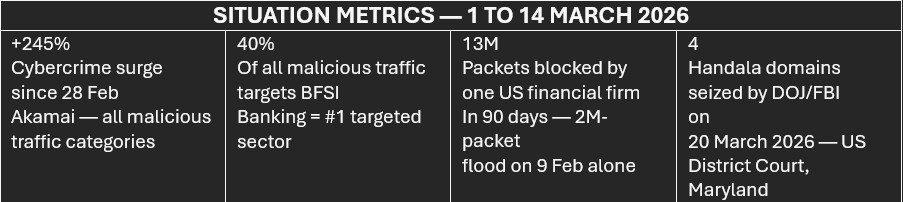
Court-authorised warrant (US District Court, District of Maryland) enables DOJ/FBI seizure of handala-hack[.]to, handala-redwanted[.]to, justicehomeland[.]org, and karmabelow80[.]org. Domains used for MOIS-directed cyberattack claims, stolen data publication, death threats to journalists/dissidents, and incitement of violence. DOJ affidavit legally confirms Handala = MOIS operation — the highestconfidence attribution event of this conflict.
2. Banking is confirmed as the #1 targeted sector globally — empirically measured, not assessed probability.
Akamai’s 16 March report records a +245% surge in total malicious traffic since 28 February. Banking and fintech absorb 40% of all malicious traffic — the largest sector share by a wide margin across all industries globally. The current activity is dominated by reconnaissance and pre-attack mapping. The destructive phase has not yet fully materialised. Organisations being scanned now face attacks later.
3. Formal regulatory action has been issued — BFSI institutions are now under documented supervisory expectation.
California Department of Financial Protection and Innovation (DFPI) and New York regulatory agencies have formally issued cyber-risk bulletins to all supervised financial institutions. CISA formally acknowledged the Stryker/Intune attack vector for the first time. Goldman Sachs has mandated prior approval for all Middle East office attendance. Standard Chartered has asked Dubai DIFC staff to work remotely. HSBC has closed Qatar branches. Citi has restricted Dubai office attendance. These are the first formal regulatory actions specifically addressing cyber risk to BFSI in this conflict. A post-conflict supervisory review of institutional cyber preparedness is near-certain.
4. Geographic and platform scope has materially expanded — no Westernaligned nation or M365-dependent entity is out of range.
313 Team executed confirmed DDoS against Microsoft 365, Outlook, and Copilot on 17 March — the first direct targeting of cloud productivity infrastructure in this conflict. South Korea targeted under #OpSouthKorea (15+ government domains including Ministry of Defence and National Intelligence Service) with no direct conflict involvement — selected purely for perceived Western alignment. Egypt’s Telecom Egypt targeted — the first North African target of the campaign, confirmed via EliteStress traffic analysis under #Op_Epstein_Gulf. 313 Team simultaneously swept 20 UAE government domains. Operational scope now confirmed across Middle East, Europe, Africa, and East Asia. Any M365-dependent BFSI entity — regardless of geography — must treat cloud productivity continuity as a live risk.
5. Legal and sanctions exposure crystallises for the first time — a new mandatory dimension for BFSI incident response planning.
Paying ransom to any Iran-aligned threat actor — including Sicarii ransomware, which permanently destroys data — may violate US IEEPA, TWEA, and OFAC SDN List regulations, even where the paying organisation is itself a victim. DOJ court documents legally confirming Handala = MOIS means any payment to Handala is an OFAC SDN List violation. EU and UK organisations face simultaneous parallel obligations: GDPR (72hr notification to supervisory authority), EU NIS2 (24hr early warning for essential services/DSPs), and UK NIS Regulations 2018. A wiper attack destroying personal data records triggers all of these simultaneously, regardless of whether any data was exfiltrated. Legal counsel must be integrated into IR escalation matrices immediately — not post-containment. This is new ground for most BFSI IR teams.
New Attack Vectors
The latest phase of activity marks a clear inflection point in how attacks are being executed. What began as disruption at the edge, through DDoS on public portals and hacktivist signalling, has now moved inward to the systems that run BFSI operations at scale. These new threat vectors aim at achieving disproportionate impact without traditional malware or noisy indicators.
Vector 1: Microsoft 365 / Cloud Productivity DDoS — NEW
What happened: 313 Team and Anti-Zionist Cyber Group claimed and confirmed DDoS disruption of Microsoft 365, Outlook, and Copilot on 17 March 2026 — the first direct targeting of cloud productivity infrastructure in this conflict. Unlike previous attacks targeting government websites and financial portals, this attack targets the shared productivity backbone used by virtually every large BFSI organisation globally.
Why it matters for BFSI: Microsoft 365 is not a peripheral system for BFSI organisations — it is core infrastructure. Teams handles internal and external communications including client-facing and regulatory correspondence. Outlook handles email including SWIFTrelated communications. Azure AD is the authentication backbone for all Azure-integrated banking systems, trading platforms, and risk management tools. A confirmed DDoS against M365 means BFSI staff could be simultaneously locked out of communications, authentication, document systems, and AI-assisted operations.
Vector 2: MDM / Microsoft Intune Console Hijack as Mass Wiper Weapon — CONFIRMED ACTIVE
What happened: Handala compromised Stryker’s Microsoft Intune MDM console and deployed a device wipe policy to 200,000+ managed endpoints across 79 countries on 11 March 2026 — sending 5,000+ employees in Ireland home and disrupting Stryker’s global operations. No malware was deployed to individual endpoints. The attack was executed entirely through legitimate Intune administrative capabilities. CISA has formally acknowledged this attack vector in a 16–17 March advisory recommending all organisations secure Intune access.
Why it matters for BFSI: Microsoft Intune manages endpoints in most large BFSI organisations. A compromised Intune administrator account provides attackers with the equivalent of physical access to every managed device — including trading workstations, payments terminals, customer service desktops, and treasury systems. The attack bypasses EDR, endpoint detection, and traditional malware defences entirely because no malware is deployed. The only defensive layer is protecting the Intune console itself.
Vector 3: Rclone + Legitimate Cloud Storage for Silent Data Exfiltration —CONFIRMED ACTIVE
What happened: MuddyWater/Seedworm used the open-source Rclone file synchronisation tool to exfiltrate data from targeted networks to Wasabi cloud storage buckets. The Fakeset backdoor was hosted on Backblaze servers. Both Wasabi and Backblaze are legitimate, commercially reputable cloud storage platforms. Their traffic is cryptographically indistinguishable from normal authorised cloud synchronisation and backup activity to most DLP, proxy filtering, and CASB solutions.
Why it matters for BFSI: This exfiltration technique evades traditional DLP controls, proxy filtering, and even many CASB configurations because the destination (Wasabi, Backblaze) is a legitimate cloud provider not typically blocklisted. Customer records, transaction data, correspondent banking information, and regulatory filings exfiltrated via Rclone to cloud storage may not trigger any security alerts at all. The pre-positioned access on a US bank (since early February) means this exfiltration may already have occurred against BFSI targets in this conflict before it was detected.
Legal and Regulatory Obligations: New Dimension for BFSI
The legal and regulatory obligations triggered by Iranian-linked cyber incidents have now been formally documented by legal practitioners including Kennedys Law (18 March 2026). BFSI legal, compliance, and IR teams must integrate these into incident response planning immediately.
1. Sanctions Violation Risk — Ransom Payments
Paying ransom to any Iran-aligned threat actor — including Sicarii ransomware, which permanently destroys data and provides no recovery path even on payment — may violate US sanctions law regardless of whether the victim organisation is US-based. The legal framework applies globally to US-person transactions and, in many cases, to non-US entities with USnexus activity (US shareholders, US cloud services, US correspondent banks, US-listed parent).
2. Data Breach & Incident Notification Obligations
A wiper attack that destroys personal data records, or a data exfiltration event, simultaneously triggers multiple notification obligations across different jurisdictions. A wiper destroying personal data constitutes a personal data breach even without exfiltration. BFSI organisations operating across the Middle East, Europe, and North America face a complex matrix of parallel, overlapping notification deadlines that must be managed concurrently from incident declaration.
Defensive Priorities
1. Treat the +245% recon surge as pre-attack groundwork — activate threat hunting immediately
Recon activity (+70% botnet discovery, +65% automated recon, +52% scanning) signals imminent attack staging.
- Launch immediate threat hunts for MuddyWater indicators
- Monitor credential stuffing across APIs, portals, and admin interfaces
2. Review and test M365/Outlook/Teams continuity plans — assume outage is real
Microsoft 365 is now a confirmed target surface.
- Validate email, Teams, and SWIFT communication failover
- Test “M365 unavailable for 4 hours” scenario (live, not theoretical)
- Ensure Azure AD fallback access works without Entra ID dependency
- Configure and test break-glass accounts (offline credentials)
3. Integrate legal counsel into the IR escalation matrix as an immediate parallel track — not a post-containment step
Legal and compliance must run in parallel with technical response.
- Notify General Counsel immediately at incident declaration
- Identify all regulatory timelines within first 2 hours
- Conduct OFAC screening before any payment decision
- Preserve forensic evidence and decision logs from the start
4. Update IR playbooks with OFAC SDN compliance requirements for ransomware response
Ransom decisions now carry legal liability, not just business risk.
- Make OFAC screening mandatory pre-payment
- Require legal sign-off as a non-bypassable gate
- Document all decisions and trigger SAR obligations where required
- Explicitly note: Sicarii-style actors destroy data regardless of payment
5. Brief physical and executive security teams on Gulf office risks — major banks are already implementing restrictions.
Banks are already restricting movement — assume operational disruption risk.
- Validate remote readiness for treasury, trading, and payments
- Update evacuation, communication, and access plans
- Ensure critical functions can run outside Gulf locations
6. Harden M365 tenants specifically against DDoS-adjacent disruption — validate fallback authentication paths.
Focus on authentication resilience and escalation readiness.
- Confirm service health monitoring and escalation paths with Microsoft
- Test access to core systems during Entra ID outage
- Review Conditional Access dependency risks
- Validate break-glass access and offline recovery paths
7. Build the regulatory evidence file now — a post-conflict supervisory review of BFSI cyber preparedness is near-certain.
Begin constructing your contemporaneous evidence file today.
- Record all actions, decisions, and briefings (time-stamped)
- Document controls implemented and tests conducted
- Track training, vendor actions, and security investments
Sources & References
- Akamai 16 March 2026 cybercrime surge report — +245% increase, full sector breakdown, source IP attribution
- Check Point Void Manticore threat intelligence report — Panjaki confirmation, Handala operational continuity analysis
- SOCRadar Iran–Israel Cyber War live dashboard — 17 March update, 313 Team / Microsoft / South Korea entries
- US DOJ press release — Handala domain seizure (20 March 2026)
- California DFPI bulletin — formal cyber-risk warning to supervised financial institutions
- NBC News / Axios (FBI/DOJ domain seizure, 20 March); Cybernews (FBI banner analysis)
- Banking Dive (DFPI/NY regulatory warnings); Euronews (Goldman / StanChart / HSBC Gulf restrictions)
- Kennedys Law — ‘Iran’s Cyber Warfare: Legal Implications for Businesses’ (18 March 2026)
 USA
USA India
India APAC
APAC Middle East
Middle East Global
Global

 Facebook
Facebook Linkedin
Linkedin  X
X Youtube
Youtube








