SISA ProACT -
Managed Detection and Response
Powered by Forensic Intelligence

Forensics-driven Managed Detection and Response service to prevent, detect and respond to threats
SISA ProACT Managed Detection and Response goes beyond traditional solutions that work on rules and signatures. Our MDR solution is powered by forensic intelligence to enable context-aware detection and response.
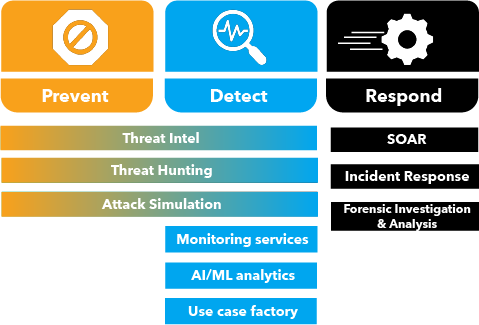
- Prevent Through advanced threat hunting guided by threat intel feeds from 70+ sources and daily actionable threat advisories, you can fortify your defences and prevent attacks.
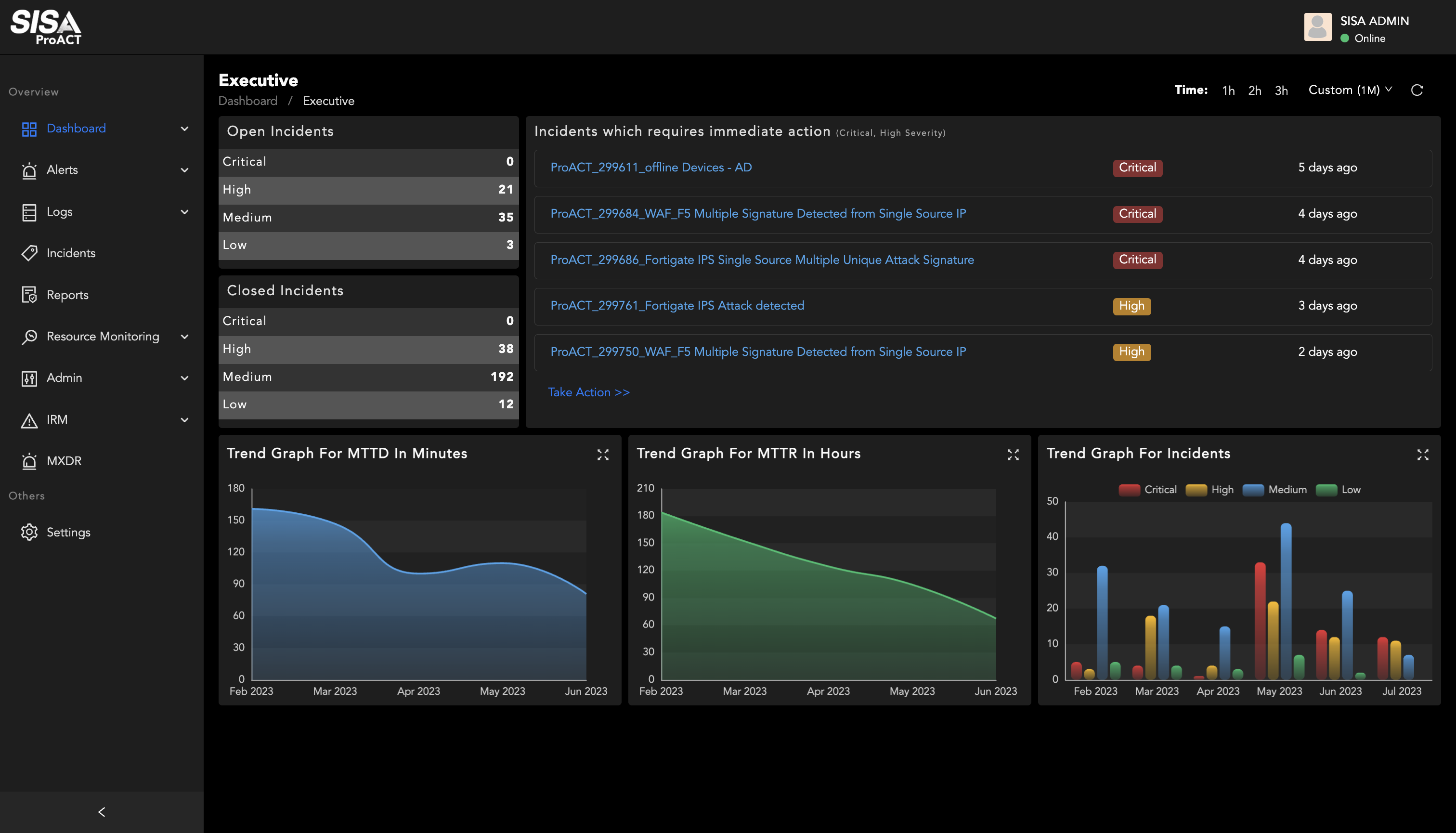
- Detect With 24/7/365 log monitoring, User Entity Behaviour Analytics, and MITRE ATT&CK based detection, you can gain greater visibility for advanced persistent threat detection.
- Respond Through managed forensics investigation and incident response, you can contain and remediate threats before they inflict damage.
A fully managed MDR service delivered by SISA’s Dedicated Team of Blue Guardians
Our SOC analysts with an average of 15+ years of experience in threat hunting techniques are a critical component of our MDR solution. Armed with forensic learnings and latest threat intelligence, they are adept in identifying and responding to security threats.

24x7x365 detection and response

Hybrid deployment models covering on-prem and cloud

Elite team of threat researchers and investigators

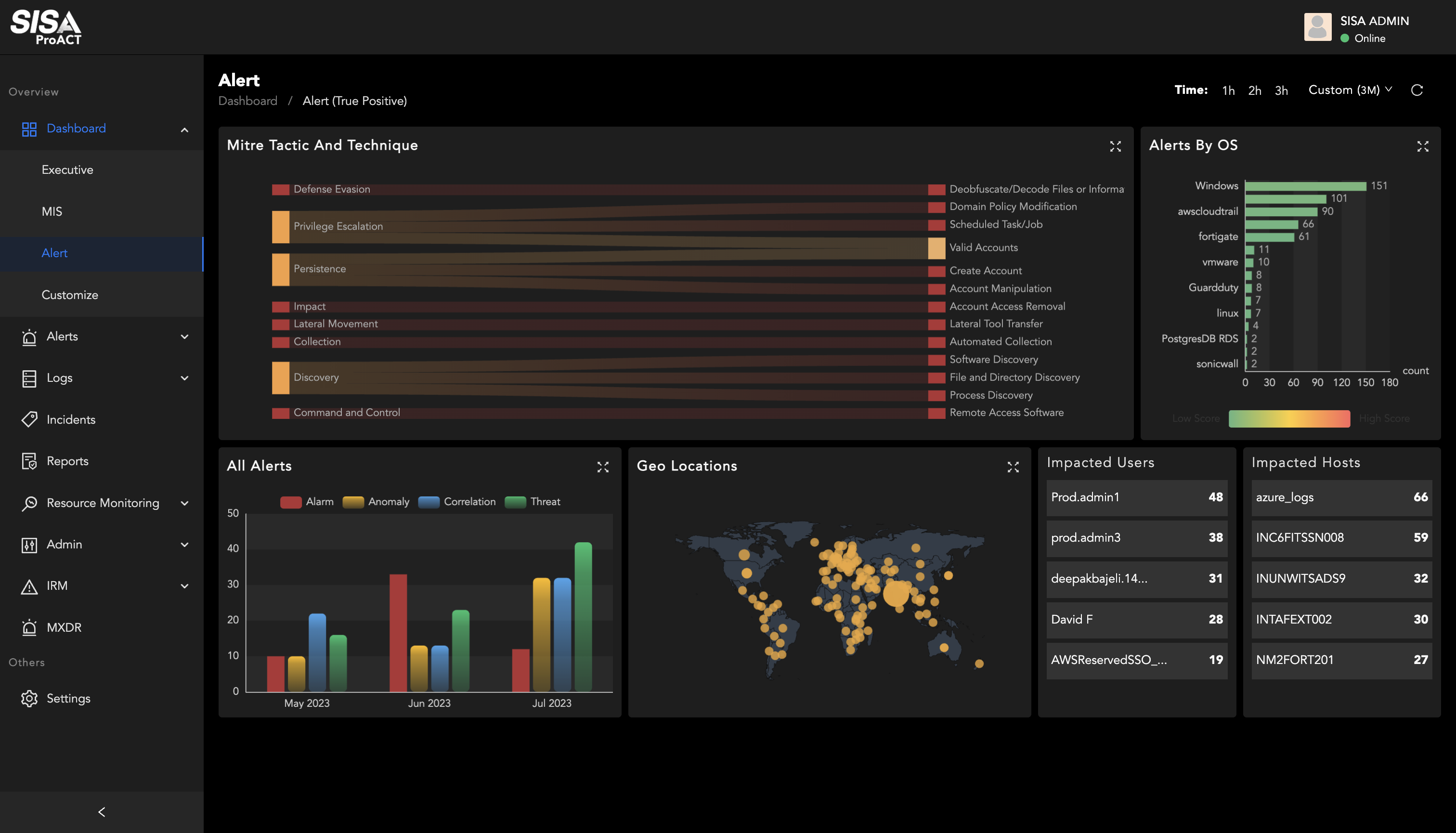
Security Orchestration, Automation and Response
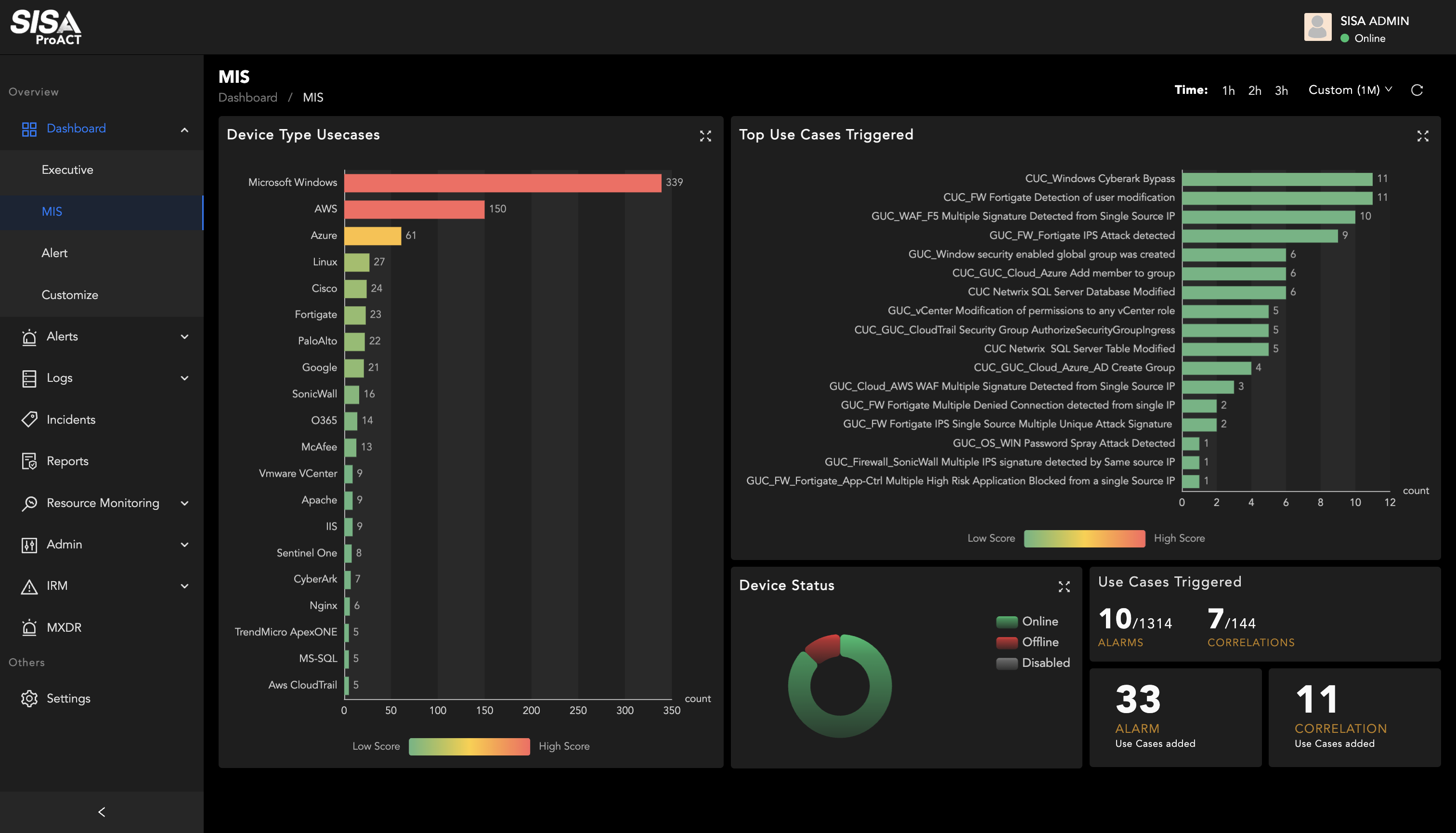
Visualize the state of enterprise security, reduce alert fatigue, and increase threat visibility
approach to reduce false positives, accelerate time to detection and lower response time.
Why choose SISA ProACT for
Managed Detection and Response?

Forensics-driven Incident Detection and Threat Hunting
Recognized as one of the top 4 global payment forensics investigators (PFIs), Inputs from our Forensics engagements are converted into Detection use cases and Threat Hunting hypotheses

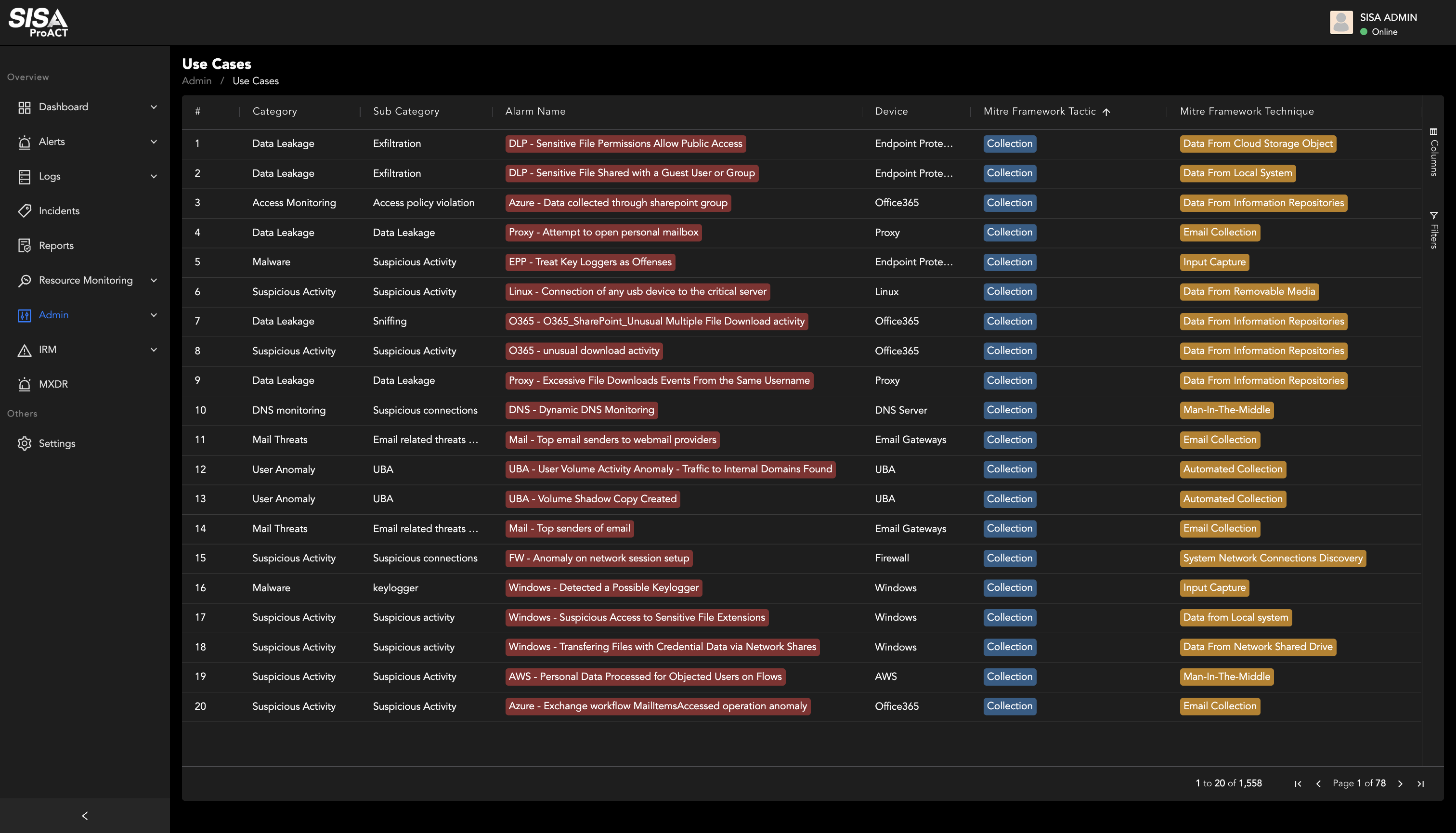
1,500+ Use cases in Library
Our SIEM Use Cases are aligned with MITRE ATT&CK framework and Sigma open standards

Automated Response
Our SOAR module uses ML models for prioritized threat detection and automated response, improving mean time to respond significantly

Actionable Threat Intelligence
1.5 million threat values from live forensic analysis, 70+Threat Intel feeds integrated into our Platform combined with actionable daily Threat Intel Advisories offer deeper insights on adversaries

SISA Training Institute
Client Teams trained on incident response & containment through our in house trainings and CIDR workshops designed and executed by SISA training Institute

IR and Forensic Support
Our MDR services also cover our flagship Incident Response and Forensic services

16+ years of Experience in Payment Industry
As a leading forensic investigator in Payment Industry, we leverage our learnings of breach investigations to improve our
preventive and detective security solutions.
An MDR solution with turnkey integration and scalability to accelerate time to value
SISA ProACT is a scalable solution that supports all platforms and deployment architectures including on-premises, cloud, co-location, and hybrid cloud deployments. Our MDR solutions facilitate faster integration with enterprise network components and scale rapidly to help you accelerate time to value.
SISA ProACT Managed Detection and Response by the Numbers
50%
Reduction in false positives
60%
Improvement in detection
30%
Reduction in mean time to respond

Cloud

On-Prem
Our MDR Services are flexible, customizable and easy on your budgets!
- Whether you are looking for a preventive cyber security solution or a comprehensive, multi-layered defense, SISA ProACT has everything in it to meet your requirement.
- Pay for what you need.
- We understand that each organization’s requirements, devices and volumes are different.
- You can choose between Standard, Advanced and Elite plans to meet your needs and volumes.

| Service | ProACT Standard | ProACT Advanced | ProACT Elite |
|---|---|---|---|
| Global 24X7X365 Monitoring | |||
| MITRE ATT&CK Framework-based Detection Rules | |||
| Automated Standard Reports | |||
| Threat Intel Advisories | |||
| Use Case Simulation | |||
| Customized Asset Integrations | |||
| Automated Response through SOAR | |||
| IR Services | |||
| Forensics Retainer Services | |||
| Audit Support | |||
| Customized Reports | |||
| CxO Ready Reports | |||
| User and Entity Behavior Analytics (UEBA) | |||
| Ransomware Simulation | |||
| Quarterly Management Review Meetings | |||
| Dedicated Relationship Manager |
Recognized by industry analysts and endorsed by customers

Rated 4.7/5 stars on Gartner Peer Insights


Ralph Aboujaoude Diaz
Practice Leader, HFS
Karl Cavanaugh
Lead Security Analyst, Club Prophet Software LLC
Hon TianYang
Vice President of Systems & Network Support, OpenSys (M) Berhad
Henry Itayi
Cyber Security Manager, NMB Bank Limited
Featured Insights
Request a Call

SISA is a global forensics-driven cybersecurity solutions company, trusted by leading organizations for securing their businesses with robust preventive, detective, and corrective cybersecurity solutions. Our problem-first, human-centric approach helps businesses strengthen their cybersecurity posture.
Industry recognition by CREST, CERT-In and PCI SSC serves as a testament to our skill, knowledge, and competence.
We apply the power of forensic intelligence and advanced technology to offer true security to 2,000+ customers in 40+ countries.
 USA
USA India
India APAC
APAC Middle East
Middle East Global
Global



 Facebook
Facebook Linkedin
Linkedin  Twitter
Twitter Youtube
Youtube